Our Technology
IKE Tech delivers end-to-end trust through two interoperable solutions - powered by Accountable and Soverign AI and secured on blockchain.
IKE’s Sovereign AI
At IKE Sovereignty in AI starts with identity.
Without verified identity and authenticated control, there’s no trust only dependency.
IKE solves this with a single architecture built on blockchain, tokenization, and de-centralized data control.
Two systems. One trust fabric. IKE
Sovereign AI


Why Identity Verification Matters
Industries face unique challenges in verifying user identity and age to prevent unauthorized access and ensure compliance with legal requirements. Traditional verification methods are often cumbersome, prone to error, and susceptible to fraud.
At IKE Tech, we address these challenges with innovative solutions that leverage blockchain based tokenized identity verification that preserves privacy while ensuring security and compliance.


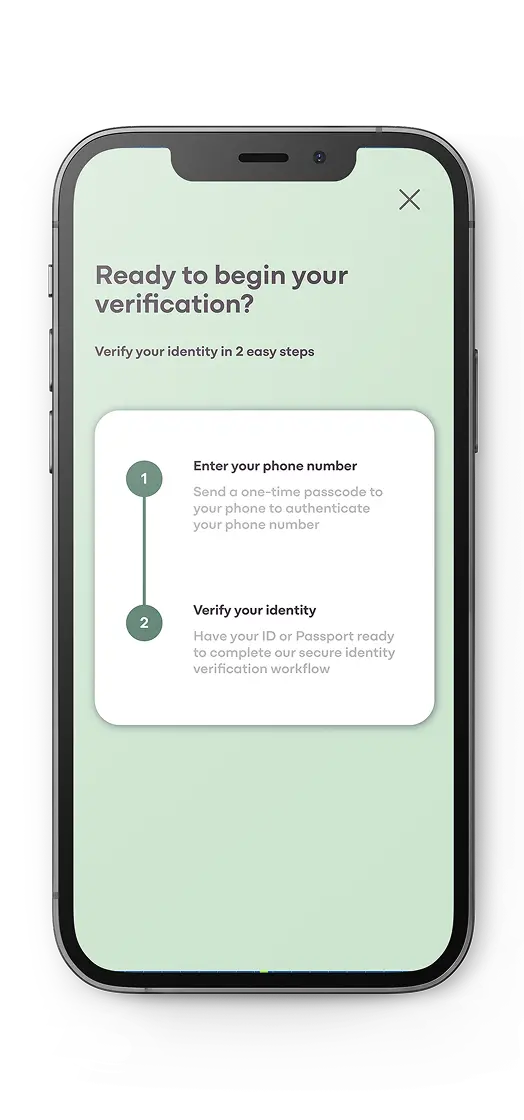
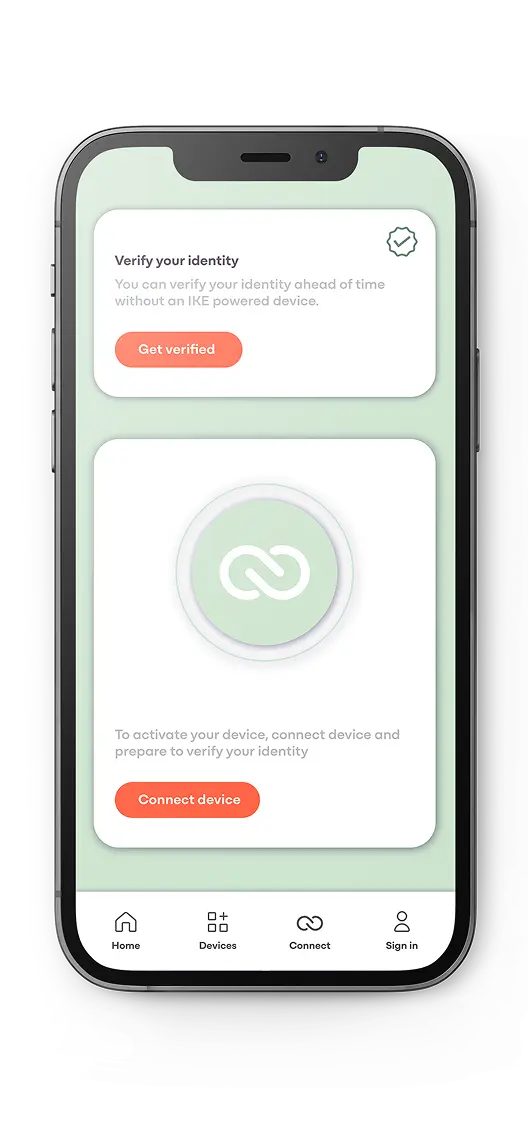
V-me is IKE Tech’s continuous identity verification system that makes access seamless, private, and secure.
By combining biometrics with our proprietary Bluetooth chip, devices remain locked until the right user is verified in real time. Unlike one-time checks, V-me enforces continuous protection while keeping personal data private through blockchain tokenization.
Key Features

Advanced Biometric Verification
Multi-layered biometric identity checks ensure only authorized users can access regulated devices, combining a live facial recognition scan and ID verification for security.

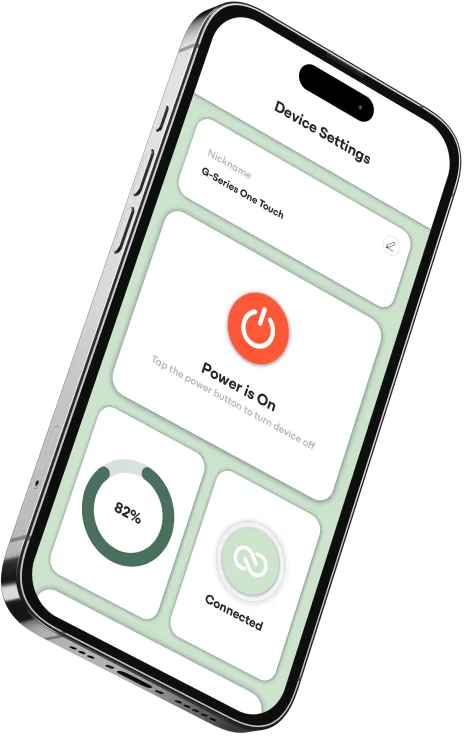
IKE Tech App (Available on iOS & Android)
Secure and manage devices seamlessly through our dedicated app on the Apple App Store and Google Play Store, delivering protection that’s always at your fingertips.

Proprietary Bluetooth Low Energy (BLE) Chip
A custom-designed chip that’s low cost, lightweight, power-efficient, and secure, enabling reliable device activation and deactivation with minimal energy use.

Patented Blockchain Security
A tamper-proof, immutable framework that safeguards devices against counterfeiting and unauthorized access, with secure device tokens stored on the blockchain to ensure authenticity and compliance. This allows verification without the storage of any personal identifiable information

Advanced Biometric Verification
Multi-layered biometric identity checks ensure only authorized users can access regulated devices, combining a live facial recognition scan and ID verification for security.

IKE Tech App (Available on iOS & Android)
Secure and manage devices seamlessly through our dedicated app on the Apple App Store and Google Play Store, delivering protection that’s always at your fingertips.

Proprietary Bluetooth Low Energy (BLE) Chip
A custom-designed chip that’s low cost, lightweight, power-efficient, and secure, enabling reliable device activation and deactivation with minimal energy use.

Patented Blockchain Security
A tamper-proof, immutable framework that safeguards devices against counterfeiting and unauthorized access, with secure device tokens stored on the blockchain to ensure authenticity and compliance. This allows verification without the storage of any personal identifiable information
Why Authentication Matters
Authenticity is the foundation of trust. Without it, counterfeit and illicit products flood markets, putting consumers at risk and eroding confidence in legitimate brands.
IKE Tech solves this with blockchain-secured authentication that delivers full traceability and accountability from manufacturer to consumer. Every product is verified in real time, creating a transparent chain of custody that blocks counterfeits, protects supply chains, and ensures that what reaches the consumer is genuine, safe, and compliant.


A-me protects products and supply chains with tamper-proof NFC/RFID smart tags secured by blockchain. Each scan instantly verifies authenticity, creating an immutable record that blocks counterfeits, tracks distribution, and builds consumer trust.
From regulated goods to consumer electronics, healthcare, and retail, A-me delivers real-time assurance that what’s in hand is genuine, safe, and transparent.
At IKE, Sovereignty in AI
starts with identity.
Without verified identity and authenticated control, there’s no trust only dependency.
IKE solves this with a single architecture built on blockchain, tokenization, and de-centralized data control.
Two systems. One trust fabric. IKE

Sovereign AI
• Learns and adapts securely
• Operates within national and enterprise data sovereignty rules
• Analyzes product anduser interactions

Identity & Accountability Tokens
• HITs (Human Identity Tokens): Verify user age and identity without revealing personal data
• AITs (AI Trace Tokens): Record and audit every AI action for full accountability

Immutable Governance
• Tamper-proof record keeping
• Distributed control across users, enterprises, and national systems.
• Compliance with EU AI Act, UAE Sovereign AI Strategy, NIST AI RMF

Key Stakeholders
• Users have privacy-protected verification• Enterprises have AI-driven compliance
• Nations have Sovereign control
• Regulators recieve transparent governance
• Ecosystem partners recieve secure interoperability